
Need to add geographic restrictions to your video content? Geo-blocking offers a way to control who is able to access your assets on a per country basis. This can be done through specific channels, allowing content owners to mix different geographic restrictions among their assets.
Recently added as an option inside IBM’s video streaming offerings, geo-blocking works across desktops and mobile devices. This includes if a viewer is trying to watch from an app. It joins a suite of security features, some of them around keeping content internal as highlighted in our Enterprise Video Security Components & Services white paper, to help enterprises keep their video content restricted to intended audiences.
- Geographic Filtering: Enabling Geo-blocking on Channels
- Viewer Experience from Geo-blocking
- Use Cases
Geographic filtering: enabling geo-blocking on channels
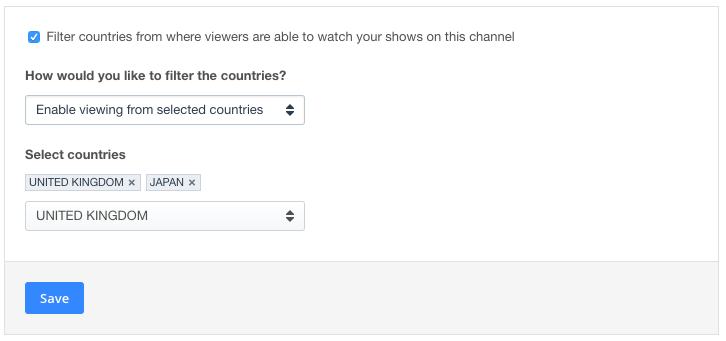
Geo-blocking can be setup on a per channel basis. This feature is controlled from a tab called “Geographic Filtering” once the channel is selected. Settings for geographic filtering will either be setup as a whitelist or a blacklist, either specifying which countries are allowed to watch or which are barred from watching.
 Whitelist:
Whitelist:
Enable viewing from selected countries
This enables content owners to select which countries are allowed to view the content on this channel. Viewers from countries not on the whitelist will be blocked from watching. This option is best suited for situations where only a few countries will be allowed to watch.
Blacklist:
Prevent viewing from selected countries
Alternatively, content owners can instead pick countries to block from viewing their content. Unselected countries will not be impacted and will be able to watch the content. Selected countries will have their viewers blocked from watching. This option is best suited for situations where only a few countries need to be blocked from viewing.
Viewer experience from geo-blocking
When someone from a blacklisted or unwhitelisted country attempts to view content on a channel they will be blocked from doing so. The exact messaging they will see inside the player will be:
“This content is not available in your area.”
Note that account administrators logged in and trying to view assets will generally not be blocked. They will still be able to watch their content. This is true even if they are coming from a country that is blacklisted or not from one of the whitelisted countries. As a result, to test geographic restrictions it’s recommended to open an incognito window in your browser. This will allow you to witness what a viewer would see from a blocked country.
Use cases
There are a variety of different use cases that can benefit from, or even mandate, the inclusion of geo-blocking. These are predominantly external stories. The reason for this is that usually internal content is already being controlled to a more specific audience. This can be done through email verification or utilizing a corporate directory. To learn about restriction options for internal content, see Streaming Manager for Enterprise. Otherwise, below are external use cases involving geo-blocking.
Concerts
Two scenarios can be involved with musical acts that involve geo-blocking. One can be that rights for broadcast distribution were negotiated for specific areas. Another scenario can be a desire to drive foot traffic from this physically close to the venue. Geo-blocking can facilitate both needs. In the instance of limited rights, a whitelist can be created noting which countries are permitted. In the instance of wanting to drive physical traffic, the country where the concert is taking place can be blacklisted.
Sports Events
Similar to concerts, sports events can go through negotiated contracts which limit where the content can be broadcast. This can be based on the locations of the teams, or more often just general regions like the rights for North America, Europe or other regions. Geo-blocking can be way to execute on these contracts, limiting viewership to the approved countries. In this case, a whitelist method would be used to select which countries are allowed to watch the content.
Demos of Geographic Specific Products
It’s possible that you have in your portfolio a product that will never come to market in a specific country. Maybe due to regulations, or a different version of the product being available there. As a result, there might be a desire to bar those who aren’t able to use the product from watching content related to it. This content can range from in-depth demos to product launches. However, it’s suggested to not do this if the product is not currently available in a country but will eventually launch there. The reason for this is that you can start to build interest and hype in those countries. So a “down the road” prospect can get excited by a product demo for when the product does eventually launch there.
Media and Entertainment
Media usage rights can often be passed through from a negotiated deal. These will often specify what markets film content, television programming and more can be distributed. Part of this distribution can involve streaming. Certain contracts might include supplement material as well, from “extras” to promotional material. Geo-blocking offers a way to execute on this. Generally usage rights specify the target market, like North America. In the example of a North America agreement, a whitelist can be setup that includes the United States, Mexico and Canada.
This list is far from inclusive. Other general uses, like for example trying to control your content to particular countries for security reasons, can also be done.
Summary
Geo-blocking provides a nice opportunity to enter into rights negotiations that include geographic limitations on distribution. Being cloud based settings, content owners can also navigate more detailed stipulations, including geographic restrictions on a live event and then removing those restrictions for its on-demand use.
For more details on restricting access to video content over IBM’s video streaming services, please reference our Video Access: Password Protection & Restriction article.
Interested in using these geo-blocking features to control the distribution of external video content?